Understanding the Laser247 Login & Signup Process: A Complete Step‑by‑Step Guide
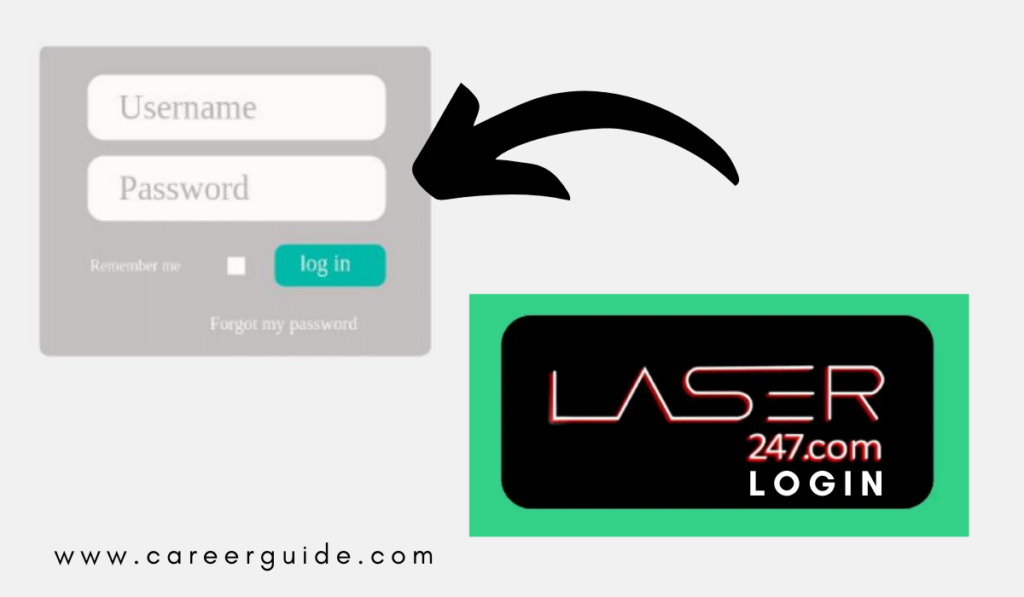
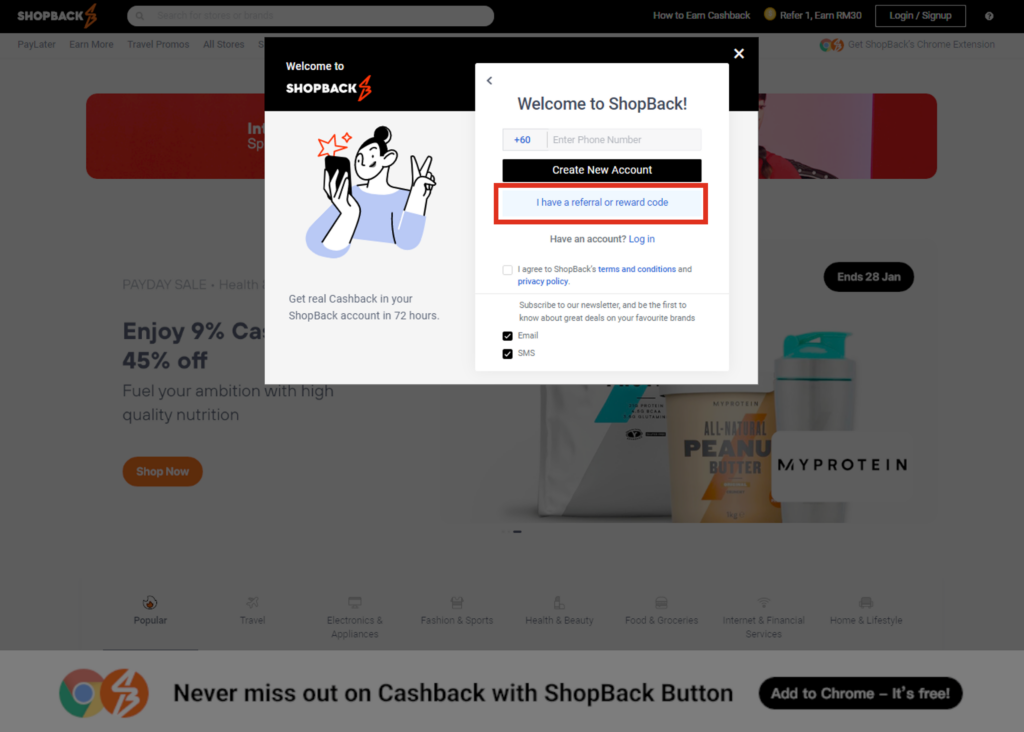
Introduction In today’s digital marketplace, platforms that deliver laser cutting and engraving services must prioritize both user accessibility and data security. Laser247 has positioned itself as a leading provider by offering a streamlined interface that balances simplicity with robust protection. Whether you are a hobbyist looking to submit a single job or a production manager handling high‑volume orders, the first interaction you have with the system—logging in or signing up—sets the tone for the entire experience. This article dissects every step of the login and signup process, highlights the technology that safeguards user data, and provides actionable advice for troubleshooting common obstacles. Why a Streamlined Login Matters A frictionless authentication flow reduces bounce rates, improves conversion, and enhances overall customer satisfaction. For service‑oriented platforms like Laser247, users often transition between design uploads, quote requests, and order tracking within minutes. Any delay or confusion at the entry point can cause users to abandon their projects, directly impacting revenue. Moreover, a well‑designed login experience conveys professionalism and trust, reinforcing the brand’s reputation in a competitive industry. Key Objectives of the Login Design Speed: Minimal page loads and rapid validation keep users engaged. Clarity: Clear field labels, error messages, and visual cues guide users intuitively. Security: Protection against unauthorized access while maintaining usability. Scalability: Ability to handle both casual users and enterprise accounts without performance degradation. Creating a New Account: The Signup Flow For first‑time visitors, the signup journey is broken into three core stages: information collection, verification, and account activation. 1. Information Collection The signup page presents a clean form that requests only essential data: full name, email address, password, and a company name (optional for individual users). Each input field incorporates real‑time validation. For example, the password field evaluates strength based on length, character variety, and common pattern avoidance, displaying a visual meter that updates instantly as the user types. To comply with global privacy standards such as GDPR and CCPA, the form also includes a mandatory checkbox where users consent to the platform’s privacy policy and receive transactional emails. This approach ensures legal compliance without overwhelming users with excessive legalese. 2. Email Verification After submitting the form, an automated email containing a unique, time‑limited token is dispatched to the provided address. The email template is minimalist, featuring the brand logo and a single call‑to‑action button labeled “Verify My Account.” Clicking the button redirects the user to a secure verification endpoint, where the token is validated. If the token is expired or altered, a friendly error page offers the option to resend the verification email. The verification step serves multiple purposes: confirming the authenticity of the email, protecting against bots, and establishing a reliable communication channel for future notifications such as order updates and promotional offers. 3. Account Activation & Initial Setup Upon successful verification, users land on an onboarding screen that walks them through optional profile enhancements. These include uploading a profile picture, linking a payment method, and setting preferred notification preferences. While optional, completing these steps unlocks advanced features like saved design templates and priority support. At the culmination of the onboarding flow, the system automatically logs the user in and redirects them to a personalized dashboard, reinforcing a seamless transition from signup to active usage. Accessing Your Dashboard: The Login Sequence Returning users encounter a concise login interface that balances speed with security. The process can be summarized in four distinct actions. 1. Credential Entry Users input their registered email address and password into clearly labeled fields. The password field incorporates a “show/hide” toggle, allowing users to verify entry accuracy without compromising security on public devices. 2. Two‑Factor Authentication (2FA) Prompt When 2FA is enabled—highly recommended for all accounts—users receive a one‑time code via their chosen method (authenticator app, SMS, or email). The interface provides a dedicated field for this code, along with a countdown timer indicating the remaining validity period. If the code expires, a “Resend Code” link appears, allowing users to request a new token without restarting the login process. 3. Session Management Options Below the credential fields, two checkboxes allow users to “Remember me on this device” and “Keep me signed in.” Selecting these options stores a secure, encrypted token in the browser’s local storage, dramatically reducing login friction for trusted devices while respecting privacy on shared or public computers. 4. Dashboard Redirection After successful authentication, users are forwarded to the main dashboard. The dashboard aggregates critical information: recent orders, quotation status, balance overview, and quick‑access shortcuts for uploading new designs. The platform’s responsive design ensures this experience remains consistent across desktop, tablet, and mobile browsers. Security Features Embedded in the Process Laser247’s login and signup workflows are fortified with multiple layers of protection, designed to mitigate both external threats and internal misuse. Encryption in Transit and At Rest All data transmitted between the client and server is encrypted using TLS 1.3, the latest version of the Transport Layer Security protocol. Server‑side, sensitive information—including passwords—are stored as salted bcrypt hashes, rendering them unreadable even if the database were compromised. Rate Limiting and Bot Detection To deter credential stuffing attacks, the platform employs adaptive rate limiting. After a predefined number of failed login attempts from a single IP address, subsequent attempts are throttled, and a CAPTCHA challenge appears. This mechanism balances user convenience with protection against automated abuse. Device Fingerprinting and Anomaly Detection Each login attempt is logged with contextual data such as device type, browser version, and geographic location. Machine‑learning models analyze patterns to flag anomalous behavior—like a login from an unfamiliar country or a new device—and trigger additional verification steps or temporary account locks. Compliance and Auditing The platform undergoes regular third‑party security audits and adheres to industry standards including ISO/IEC 27001. Detailed audit logs are retained for at least twelve months, allowing administrators to trace any suspicious activity with precision. Common Issues and Troubleshooting Even with a refined process, users may encounter obstacles. Below are the most frequent challenges and recommended resolutions. Forgotten Password By clicking the “Forgot password?” link on the